A Guide For Keeping Your Kids Safe Online

Parents and all who are concerned about the well-being of our young kids in this digital world.
Today we will discuss a topic of utmost importance: digital safety for kids.
Yes, the Internet can be a very dangerous place for our young kids , especially with the spread of phishing scams.
So, let us dive deeper and present to you, in this comprehensive article, a comprehensive guide on digital safety for kids.
What every parent needs to pay attention to.
Internet risks for kids:
The internet has become a big part of our kids lives.
I mean, seriously, these days it seems like kids are born with smartphones in their hands, doesn’t it?
From playing games to chatting with friends, watching videos, and doing homework – the internet is everywhere, and our children are right during it.
But with all the fun and useful things the internet offers, there are also some very serious risks lurking there.
Cyberbullying: Children are subjected to bullying by their peers online, which can cause them significant psychological and emotional harm.
Inappropriate Content: Children can easily find inappropriate content online with just a few clicks, which can negatively impact their growth and development.
Identity Theft: Children may fall victim to identity theft, where hackers gather their personal information and use it for unlawful purposes.
Online Scammers: Children may encounter scammers who pretend to be someone else with the intention of exploiting or harming them.
Internet Addiction: Children may spend excessive time online, which can affect their studies, social relationships, and physical and mental health.
What can we do to keep children digital safe?
Alright, to start with, there are some measures we can take to protect them, and the most important ones include:
Communication with your children: Talk to your children about the risks of the internet and how to stay safe online.
Establish clear rules. Set rules for internet usage, such as how much time they can spend online and which websites they can visit.
Use parental control tools: Utilize parental control tools to restrict access to inappropriate content and monitor your children’s online activities. Google offers parental control services for its products, which you can explore here.
Set a good example: Be a good role model for your children by using the internet responsibly.
Remember, “If we’re always glued to our screens, our children will think this is normal and will do the same!”
Encourage positive internet use: Encourage your children to use the internet positively for learning, creativity, and connecting with others.
In conclusion,
I would like to remind you that ensuring children’s digital safety is everyone’s responsibility, and through working together, the internet can be a wonderful place for children to learn, explore, and communicate with others—as long as we help them stay safe along the way.
So, let’s come together and ensure the safety of our little ones, and the future of our nation.
Let’s all make sure that our young internet explorers can navigate the online world confidently and cautiously by promoting a culture of cybersecurity awareness!
Share this article:
Popular
Major Data Leak Exposes 183 Million Email Accounts – What Happened and What It Means
Major Data Leak Exposes 183 Million Email Accounts – What Happened and What It Means A massive data leak came to light on October 28, 2025, with reports confirming that hundreds of millions of user credentials have been exposed online. Below, we break down the key facts of this breach – including its source, scale, and implications – and then explore how cybersecurity solutions from Cerebra.sa could help prevent or mitigate such incidents in the future. Overview of the October 28, 2025 Data Leak Source/Target: The breach did not stem from a single company hack, but rather from a trove ...
29th Oct 2025
Top 3 Phishing Types and How to Prevent Them in 2025
Phishing Types: Spear Phishing, Smishing & How to Avoid Phishing Emails The Enduring Threat: Why Phishing Attacks Are Getting Smarter Phishing types like spear phishing, smishing, and whaling are becoming more sophisticated in 2025, making it harder than ever to avoid phishing emails. This guide explores the most dangerous phishing types and shows you how to recognize and prevent them before they cause harm. The National Cybersecurity Authority (NCA) reinforces this urgency with its awareness message: ‘Stop for 5 seconds… Guard Your Cyberspace.’ What Is Phishing? Definition and Modern Tactics Phishing is a cyberattack where malicious actors impersonate trusted ...
5th Aug 2025
5 Critical Benefits of AI in Cybersecurity: Latest Data and Threat Defense in 2025
Using AI in Cybersecurity We should start learning using AI in cyber security because Hackers aren’t going to slow down any time soon and with a using AI! The next step to level up in protecting your business’s IT infrastructure is to integrate artificial intelligence. Studies have revealed that AI will strengthen the wall between systems and cyber threats. According to an IBM report, the global average cost of a data breach in 2025 is $4.4 million. Even though, it decreased by 9% vs previous year, the numbers are still way higher than few years back. They are elevating their approaches ...
1st Aug 2025
6 benefits of SMS Marketing you should know!
6 benefits of SMS Marketing you should know! Have you ever used SMS marketing to reach and communicate with your audience, if not! I’m sure that you will change your mind when you read about the benefits of SMS Marketing, continue this article to learn.. Many businesses are constantly seeking ways to interact with and attract new customers. Their joint objective is to reach a wider audience. To do so, communication is key. There are many ways for businesses to communicate with their audience, either by email, social media, or adverts, but the most beneficial marketing method, that is often ...
30th Jul 2025
MFA: the New Firewall In the 21st century
MFA- Multi Factor Authentication This article will help you to understand why Multi Factor Authentication( MFA )became an important architectural component in protecting us in the new Working From Home. Introduction In the early days, Cybersecurity (then called IT Security or information security) used to be merely a username and password. If you ask to someone, they would say I have a username and password so I am safe. It wasn’t much of the internet at that time. Eventually, people have learned that password isn’t sufficient to protect their digital assets. So Antivirus (AV) software flourished and we saw a ...
20th Jul 2025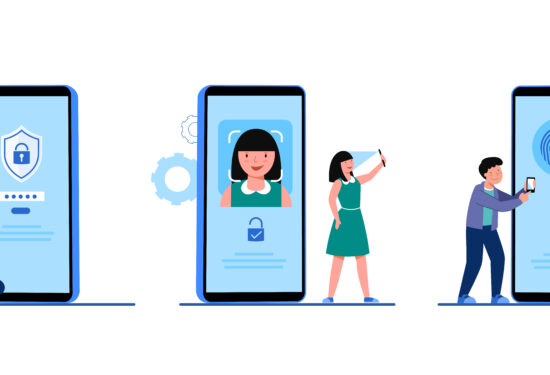
What is the role of MFA? |ECC & SAMA Compliance
ECC & SAMA Compliance with MFA solution Do you know that there are a great MFA solutions in market today help your organization for ECC & SAMA Compliance? this article will show you how and we will provide you the most incredible MFA solution help to comply with Cybersecurity regulation in KSA.. With the world of cyber threats becoming more intense than ever, organizations need to comprehend the need for an improved cybersecurity framework. The universal goal is to protect the organization’s network from any outsider or insider threats, especially with the addition of remote work resulting from the COVID-19 ...
15th Jul 2025
The AI Revolution in Cybersecurity: A New Frontier of Defense
The AI Revolution in Cybersecurity: A New Frontier of Defense How is AI revolutionizing the cybersecurity industry? The rapid evolution of Artificial Intelligence (AI), especially with the rise of Generative AI (GenAI), is not just reshaping every industry; it is fundamentally transforming how we approach digital defense. As cyber threats grow in complexity and scale, AI is emerging as a powerful ally, offering innovative solutions to protect digital assets and infrastructure. For a full list of advantages, read about the 5 Benefits of Using AI in Cyber security. At Cerebra, we explore how AI is reshaping the cybersecurity landscape—from enhancing ...
6th Jul 2025
Uber security breach by 18-year-old Hacker!
Uber security breach by 18-year-old Hacker! Uber security breach proves that the largest companies can be hacked by teenagers! this news will undoubtedly shock you.. How Uber security breach happened? Uber recently experienced a cyberattack where an 18-year-old hacker accessed their systems by launching a successful social engineering attack on an employee. The hacker used stolen employee credentials to launch an MFA (Multi-Factor authentication) Fatigue attack. It is an attack where a victim receives multiple requests from their MFA application till it bothers them out leading them to eventually accept the request. The teenage attacker did not disclose how he ...
15th Jun 2025
Biometric Authentication: Is it reliable?
Biometric Authentication The history of bio-metrics used as an authentication tool dates to the 1800s. It was first used by the French to identify criminals through their fingerprints, which later the English police commissioner, Edward Henry, developed HCS “Henry Classification System”. It was a system that relied on fingerprints to identify people who have been prosecuted, it was a prime way of classification used by the police during the 20th century. As the years continued, new biological traits started being used in biometric authentication which in result are replacing traditional methods of authentication. Any invention introduced in the cyber world ...
10th Jun 2025