ECC & SAMA Compliance with MFA solution
Do you know that there are a great MFA solutions in market today help your organization for ECC & SAMA Compliance? this article will show you how and we will provide you the most incredible MFA solution help to comply with Cybersecurity regulation in KSA..
With the world of cyber threats becoming more intense than ever, organizations need to comprehend the need for an improved cybersecurity framework. The universal goal is to protect the organization’s network from any outsider or insider threats, especially with the addition of remote work resulting from the COVID-19 pandemic. Not to mention the recent rise in online fraud, which largely stems from phishing attacks in financial and e-commerce transactions.

Being dependent solely on usernames and passwords to secure access and data is outdated, as 61% of organizations’ data breaches were a result of stolen employee credentials. Traditional methods are not capable anymore of achieving efficient results in securing an organization’s infrastructure.
Employees who are now working remotely, are accessing data and servers from different locations and using personal devices, which results in less visibility and control of user access activity.
As the name suggests, Zero Trust approach treats every activity as a hostile attempt. Meaning it requires authentication and authorization for all users and devices, whether they are inside or outside the organization’s network perimeter, to access servers, applications, and data. To enable this digital transformation, multi-factor authentication (MFA) is a crucial component of this architecture.
How can MFA help in ECC & SAMA Compliance?
Multi-factor authentication (MFA) is now considered the new firewall, where it adds an extra layer of protection to your IT infrastructure. MFA is a verification approach that requests multiple types of authentications before the user gains access to the intended data. Such verification can be done either by entering a one-time code received by email, SMS, or push notifications, approving access from an MFA application, or through biometrics. Each of these MFA requests are only valid for a single session, making it difficult to impersonate a trusted device, identity, or network.
MFA can also help in increasing the trust level between machines and systems. For instance, by using Geolocation information the authentication system can identify if the access request is malicious. For example, if a user logs in to systems from an unfamiliar country other than where the user usually logs in from, it will block that attempt.
With remote work and cloud servers becoming the prime focus of organizations, this emphasized the necessity for a secure work environment. And with the Zero Trust approach, organizations can protect all user and device connections across their network, including IoT, and secure all connections within cloud servers to ensure that only authorized users and secure devices can access them.
There are countries that have made securing their digital assets a priority, and Saudi Arabia is one of them.
Saudi Arabia Cybersecurity Compliance (ECC & SAMA Compliance)
In Saudi Arabia, and as part of the Saudi Vision 2030, where the government is actively pushing to become a digitized society, regulators such as the Saudi National Cybersecurity Authority (NCA) and The Central Bank (SAMA) have developed cybersecurity compliance frameworks that adopt the Zero Trust model. It can improve trust in electronic services for banking and government.
The Essential Cybersecurity Controls (ECC) from NCA and SAMA Cybersecurity framework (SCF), which are based on industry cybersecurity standards such as ISO and ISF, emphasize the importance of permitting authorization to access the organization’s networks and data based on confirmed and trusted identities. It now mandates critical infrastructures to apply cybersecurity controls such as MFA, Privilege Access Management (PAM), and Identity Access Management (IAM) to achieve compliance.
The kingdom of Saudi Arabia has been ranked second place globally in the cybersecurity index within the World Competitiveness Yearbook (WCY) for 2022. This achievement verifies the effectiveness of the cybersecurity initiatives taken by the Kingdom. And In order to manage and withstand the increasing cyber security threats, organizations must achieve a sufficient level of security, implementing the Cybersecurity Framework is the first step.
As one of the world’s noted cybersecurity experts John Kindervag once said, Never trust; Always verify.
READY TO TAKE THE NEXT STEP?
We at Cerebra can help you achieve ECC and SAMA compliance with our ultimate multi-factor authentication solution mPass and to help you secure your organization’s assets!
Share this article:
Popular
Major Data Leak Exposes 183 Million Email Accounts – What Happened and What It Means
Major Data Leak Exposes 183 Million Email Accounts – What Happened and What It Means A massive data leak came to light on October 28, 2025, with reports confirming that hundreds of millions of user credentials have been exposed online. Below, we break down the key facts of this breach – including its source, scale, and implications – and then explore how cybersecurity solutions from Cerebra.sa could help prevent or mitigate such incidents in the future. Overview of the October 28, 2025 Data Leak Source/Target: The breach did not stem from a single company hack, but rather from a trove ...
29th Oct 2025
Top 3 Phishing Types and How to Prevent Them in 2025
Phishing Types: Spear Phishing, Smishing & How to Avoid Phishing Emails The Enduring Threat: Why Phishing Attacks Are Getting Smarter Phishing types like spear phishing, smishing, and whaling are becoming more sophisticated in 2025, making it harder than ever to avoid phishing emails. This guide explores the most dangerous phishing types and shows you how to recognize and prevent them before they cause harm. The National Cybersecurity Authority (NCA) reinforces this urgency with its awareness message: ‘Stop for 5 seconds… Guard Your Cyberspace.’ What Is Phishing? Definition and Modern Tactics Phishing is a cyberattack where malicious actors impersonate trusted ...
5th Aug 2025
5 Critical Benefits of AI in Cybersecurity: Latest Data and Threat Defense in 2025
Using AI in Cybersecurity We should start learning using AI in cyber security because Hackers aren’t going to slow down any time soon and with a using AI! The next step to level up in protecting your business’s IT infrastructure is to integrate artificial intelligence. Studies have revealed that AI will strengthen the wall between systems and cyber threats. According to an IBM report, the global average cost of a data breach in 2025 is $4.4 million. Even though, it decreased by 9% vs previous year, the numbers are still way higher than few years back. They are elevating their approaches ...
1st Aug 2025
6 benefits of SMS Marketing you should know!
6 benefits of SMS Marketing you should know! Have you ever used SMS marketing to reach and communicate with your audience, if not! I’m sure that you will change your mind when you read about the benefits of SMS Marketing, continue this article to learn.. Many businesses are constantly seeking ways to interact with and attract new customers. Their joint objective is to reach a wider audience. To do so, communication is key. There are many ways for businesses to communicate with their audience, either by email, social media, or adverts, but the most beneficial marketing method, that is often ...
30th Jul 2025
MFA: the New Firewall In the 21st century
MFA- Multi Factor Authentication This article will help you to understand why Multi Factor Authentication( MFA )became an important architectural component in protecting us in the new Working From Home. Introduction In the early days, Cybersecurity (then called IT Security or information security) used to be merely a username and password. If you ask to someone, they would say I have a username and password so I am safe. It wasn’t much of the internet at that time. Eventually, people have learned that password isn’t sufficient to protect their digital assets. So Antivirus (AV) software flourished and we saw a ...
20th Jul 2025
The AI Revolution in Cybersecurity: A New Frontier of Defense
The AI Revolution in Cybersecurity: A New Frontier of Defense How is AI revolutionizing the cybersecurity industry? The rapid evolution of Artificial Intelligence (AI), especially with the rise of Generative AI (GenAI), is not just reshaping every industry; it is fundamentally transforming how we approach digital defense. As cyber threats grow in complexity and scale, AI is emerging as a powerful ally, offering innovative solutions to protect digital assets and infrastructure. For a full list of advantages, read about the 5 Benefits of Using AI in Cyber security. At Cerebra, we explore how AI is reshaping the cybersecurity landscape—from enhancing ...
6th Jul 2025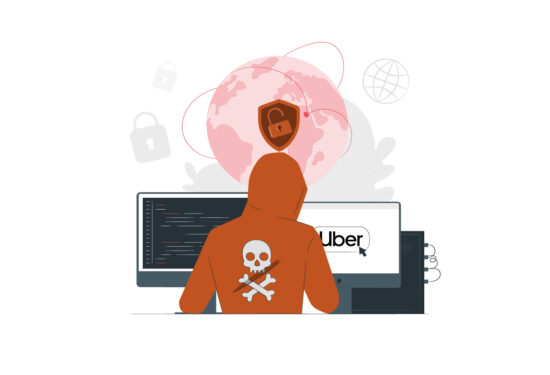
Uber security breach by 18-year-old Hacker!
Uber security breach by 18-year-old Hacker! Uber security breach proves that the largest companies can be hacked by teenagers! this news will undoubtedly shock you.. How Uber security breach happened? Uber recently experienced a cyberattack where an 18-year-old hacker accessed their systems by launching a successful social engineering attack on an employee. The hacker used stolen employee credentials to launch an MFA (Multi-Factor authentication) Fatigue attack. It is an attack where a victim receives multiple requests from their MFA application till it bothers them out leading them to eventually accept the request. The teenage attacker did not disclose how he ...
15th Jun 2025
Biometric Authentication: Is it reliable?
Biometric Authentication The history of bio-metrics used as an authentication tool dates to the 1800s. It was first used by the French to identify criminals through their fingerprints, which later the English police commissioner, Edward Henry, developed HCS “Henry Classification System”. It was a system that relied on fingerprints to identify people who have been prosecuted, it was a prime way of classification used by the police during the 20th century. As the years continued, new biological traits started being used in biometric authentication which in result are replacing traditional methods of authentication. Any invention introduced in the cyber world ...
10th Jun 2025
6 Tips to create a strong password easily!
Create a strong password easily! Today it’s very important to everyone who have an account either on social media or any other websites or services to Create a strong password, because you have to treat your password as your best stuff’s and protect it from others. Learn now the easiest and best tips you have to follow to make a strong password.. What is Password? A password is a string of characters that provides access to a digital system or service. It is a crucial security measure that helps to protect sensitive information from unauthorized access. Passwords can be as simple as a word ...
1st Jun 2025